Email remains a crucial communication channel for most personal and business users, and its effectiveness can be further enhanced with a Web Design service. Be it exchanging updates across teams, sharing your next big confidential business proposal, sending out reminders to colleagues or asking for feedback from a client, email acts as a critical lifeline. Nonetheless, email security has grown to be ever more crucial as a range of cyber threats focus on email systems. The tightest email security protocols help you not only safeguard sensitive information but also preserve trust, adhere to regulations and remain operational.
The Significance of Email Security
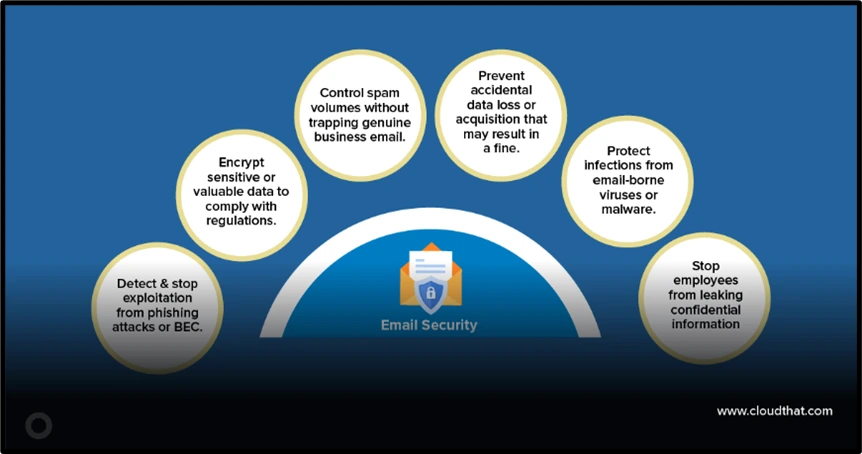
True that digital transformation has brought unprecedented convenience, but together with this, an upsurge in the routes cybercriminals may infiltrate our business. Phishing, malware distribution, and business email compromise (BEC) are some of the most common forms of cyber threats — 9 out of 10 include an email-based attack. Essentially, the value of email security is in its ability to deflect these attacks, saving organizations from loss of money or compromised reputation as well as regulatory fines.
Email is just access to critical systems and data. The outlook is grim, even when just user credentials are involved, let alone sensitive documents. The importance of email security for businesses — Email security has gone from being just a good idea to an existential necessity, as the stakes (risks) have continued to increase.
For instance, a finance department member falling foul of a phishing scam, resulting in funds being transferred to an attacker’s account. For example, those incidents can be a great loss for the company in terms of money and its reputation.
Common Threats That Make Email Security Crucial
To appreciate the importance of email security, it’s essential to understand the threats organizations face. Phishing remains the most persistent. Starting as seemingly legitimate emails from anyone with bad intentions to lure unknowing individuals into revealing sensitive information. Finally, there are the ransomware campaigns, which silently infect ecosystems only to hold sensitive info hostage for a fee. This is compounded by the ever-increasing menace of email spoofing and impersonation, which can catch even the most cautious users out.
Such as the 2021 Colonial Pipeline ransomware attack. Hackers access via a broken email account. If you need any proof of just how important email security is, consider the fact that this one breach shut off a pipeline of fuel to the U.S. East Coast, leaving countless gas pumps dry. This is especially critical for small and medium-sized enterprises (SMBs), where it is known that the presence of proactive defences against malware, ransomware and other threats can make all the difference. Strict email security protocols can reduce the dangers posed by this trend.
The Core Components of Email Security
Encryption as a Fundamental Layer of Protection
One of the most effective ways to safeguard sensitive information in emails is through encryption. Encryption ensures that the content of emails remains unreadable to anyone who intercepts them. Even if an attacker gains access to an email, encrypted data will appear as incomprehensible gibberish without the appropriate decryption key. Both Transport Layer Security (TLS) for email transmission and end-to-end encryption for sensitive communications are critical.
For instance, medical organizations subject to regulations like HIPAA must use encryption to protect patient data. Without it, emails containing sensitive health information could be exposed during transmission, resulting in breaches and hefty fines.
Implementing Multi-Factor Authentication (MFA)
User authentication is another pillar or group in Email security. In the current threat landscape, passwords are not enough. For example, this authenticator can be a form of multi-factor authentication (MFA), making it far less likely that an unauthorized party would gain access to an account. Even if a password gets leaked, with MFA, attackers have to work harder to overcome that.
In fact, in 2021, Google ordered MFA for more than 150 million accounts — and that led to a 50% drop in breached accounts. Organizations would benefit from mandating MFA for all email platforms.
Threat Detection and Monitoring
Sophisticated threat detection tools scrutinize email traffic, looking for anomalies, verifying attachments and links for any concerns. Current email security systems apply artificial intelligence to detect these threats on the fly. They can identify unexpected logins, with warning signs raised for potential phishing emails, and automatically redirecting harmful messages into the spam folder.
Develop a technical control to address this, AND develop ways to inspect for organizational awareness. Teaching employees how to spot fake email addresses, the strange requests, and bogus links is an extra quick layer of security.
The Role of Employee Education in Email Security
Human error is still the weakest link in email security, even as technical defences are essential. According to a 2023 Verizon report, human elements caused up to 74% of data breaches, wherein people clicked on malware links or downloaded weaponized attachments. Employee training can not be overlooked to mitigate threats from email.
Training regimens that address phishing awareness, email safety tips, and simulated attacks can give teams the skillsets to stay ahead of expensive mistakes. There are a lot of good reasons for companies that want educated workers to help educate those workers. For example, one large financial institution saw phishing-related incidents reduced significantly following twice-yearly staff training on email security.
One should never stop learning, as education is a continuous process. Because threats are always changing, the training employees receive should be updated as new techniques are discovered and employed by cyber attackers. With knowledge of spear phishing and the dozens of other threats employees are subjected to, knowing how email spoofing presents itself is one line of defence.
Regulatory Compliance: The Email Security Factor
In protecting your sensitive data, email security also plays a major role in meeting regulatory requirements. Virtually every industry has its own data protection laws that companies must follow in the management of emails. Ignoring any of this guidance will bring down brutal punitive measures.
For instance, look at Europe’s GDPR (General Data Privacy Regulation); Breaking the General Data Protection Regulation (GDPR) data breach notification rules can cost organizations up to 4 per cent of their annual global revenue. Likewise, in the United States, there are federal laws (e., the Sarbanes-Oxley Act) that require email security to be implemented according to certain criteria in some industries such as finance and healthcare.
For compliance to be assured, organizations must undergo periodic audits of their email practices, encrypt all communications and demonstrate a clear chain of procedures in case of security breaches. Then email protections are taught out to the company from disruptive hackers, so that the computer system can be avoided and legal claims.
Actual Use Case of Email Security Filters
Email security is not only about preventing anyone from getting in, but also about ensuring that the information is secure. Trust and Confidence: A secure email system helps in building trust with your clients, partners and employees. When stakeholders have confidence that an organization is active in protecting sensitive communications, they are more apt to reach out.
Email security protects organizations from operational downtime. Ransomware cyberattacks can make email systems inoperable, thereby disturbing business continuity. The 2020 attack on software company SolarWinds is an illustration of unsafe email communications. That resulted in months of remediation and lost time for its clients. Use rock-solid email security to create tougher systems as well – systems that can weather the harshest storms and come out fine.
This is also somewhat financially motivated. The GHIDRA approach is also similar to the Los Alamos National Lab and MIT Lincoln Labs sponsored cyber program, they find the attacks follow a financial pattern –sophisticated attacks cost $150 -200K to launch needing experts in six figure salaries plus access( these are impossible to stop but should be found after or during) simple fixes like DMARC monitoring can significantly cut 90% of email threats requiring only several hours set up and $3K annual running. In IBM’s 2023 report, which apparently gives four years of data breach costs, it lists the global average cost of a compromised email system as $4.45m. The return on investment achieved by such strong email security is too valuable a safeguard to ignore.BackgroundImage Before one takes an attempt at anything, the alarming study about the statistically possible event of cybercrime haunts.
How to start improving email security
As a result, the best place to start is frequently with a layered strategy. Start by assessing existing vulnerabilities and determining where encryption protocols, user authentication, and monitoring tools can be introduced. The golden rule is that you should always use industry-standard solutions for business operations, such as a secure email gateway, and set solid policies on how the email should be used by end-users.
The least we could do is to invest in employee awareness campaigns. However, with humans being human, no amount of technology will be immune to glitching. CISO and IT teams can collaborate to combat the perception that email security is solely an administrative burden.
Lastly, be aware of the ever-changing email-threat environment for organizations. Stay on top of the latest cybersecurity trends by subscribing to cybersecurity-based newsletters and webinars, and participating in forums relevant to your industry.
Final Thoughts
It is really crucial to secure an email in a digitalized world as we all use email for communication. Sorry to break it to you, but protecting sensitive data is not just about installing firewalls or spam filters — it includes encryption, authentication, threat detection and user awareness!
With a potent email protection solution, companies can reduce the liability and be compliant & provide trust to those they are dealing with. This safeguards the data but also enables organizations to succeed in a time when cybersecurity is one of the most important factors in success.